
The Rise of AI-Powered Threat Detection: What You Need to Know
Discover how artificial intelligence is revolutionizing cybersecurity threat detection and why traditional approaches are becoming obsolete.



Stay informed with our latest articles on cybersecurity threats, best practices, and industry trends

Discover how artificial intelligence is revolutionizing cybersecurity threat detection and why traditional approaches are becoming obsolete.
Ransomware remains one of the most damaging cyber threats. Learn the essential strategies to protect your organization.

Navigate POPIA requirements with our comprehensive guide to data protection compliance in South Africa.

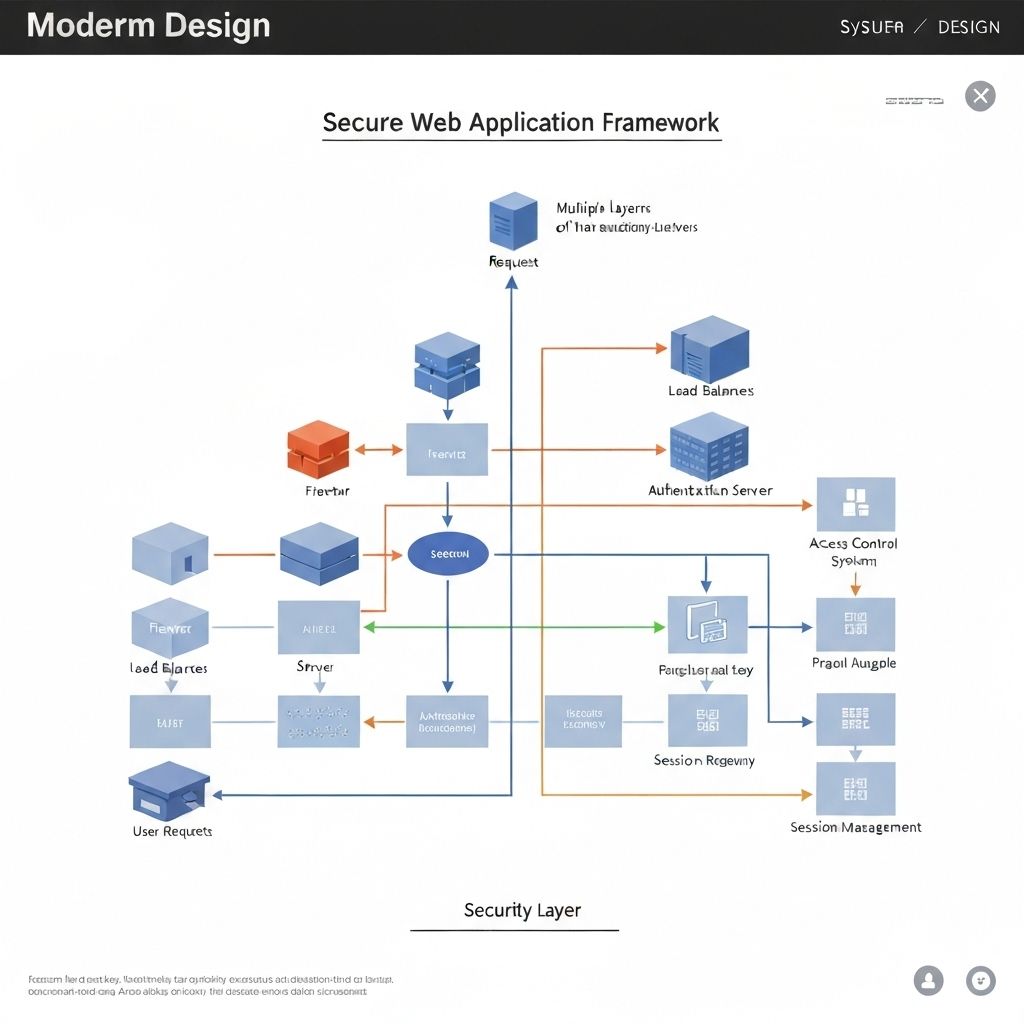
Zero Trust architecture assumes no user or device can be trusted by default. Learn how to implement this model in your organization.

Cloud environments present unique security challenges. Discover essential best practices to secure your cloud infrastructure.

A well-prepared incident response plan can minimize damage from security breaches. Learn how to develop an effective strategy.
Subscribe to our newsletter for weekly updates on cybersecurity trends, threat intelligence, and industry best practices delivered straight to your inbox.
No spam, unsubscribe anytime. We respect your privacy.
Our cybersecurity experts are ready to help you implement the strategies discussed in our research.